Remove Subresource Integrity (SRI) from the GOV.UK assets domain
Note: This is an RFC I wrote to persuade the GOV.UK Senior Technology team to remove Subresource Integrity (SRI) from the assets served from the assets domain of GOV.UK, thus enabling better performance for the HTTP/2 protocol. It was originally posted on the GOV.UK RFCs GitHub repo. It can be viewed here. I’m posting it to my blog so as to own my own work and hopefully give it more visibility. I wrote a blog post about the changes but the content was deemed too technical for the “Technology in Government blog”, so I pushed for it to be published as a case study instead, which can be seen here. I also wrote about this issue on my personal blog the post is called HTTP/2 and Subresource Integrity don’t always get on.
Summary
Due to the security requirements of SRI, crossorigin="anonymous" is required for these assets. This forces browsers to open a separate TCP connection to download this resource. Since TCP connections are expensive to open and maintain, this practice has a negative effect on frontend performance.
Problem
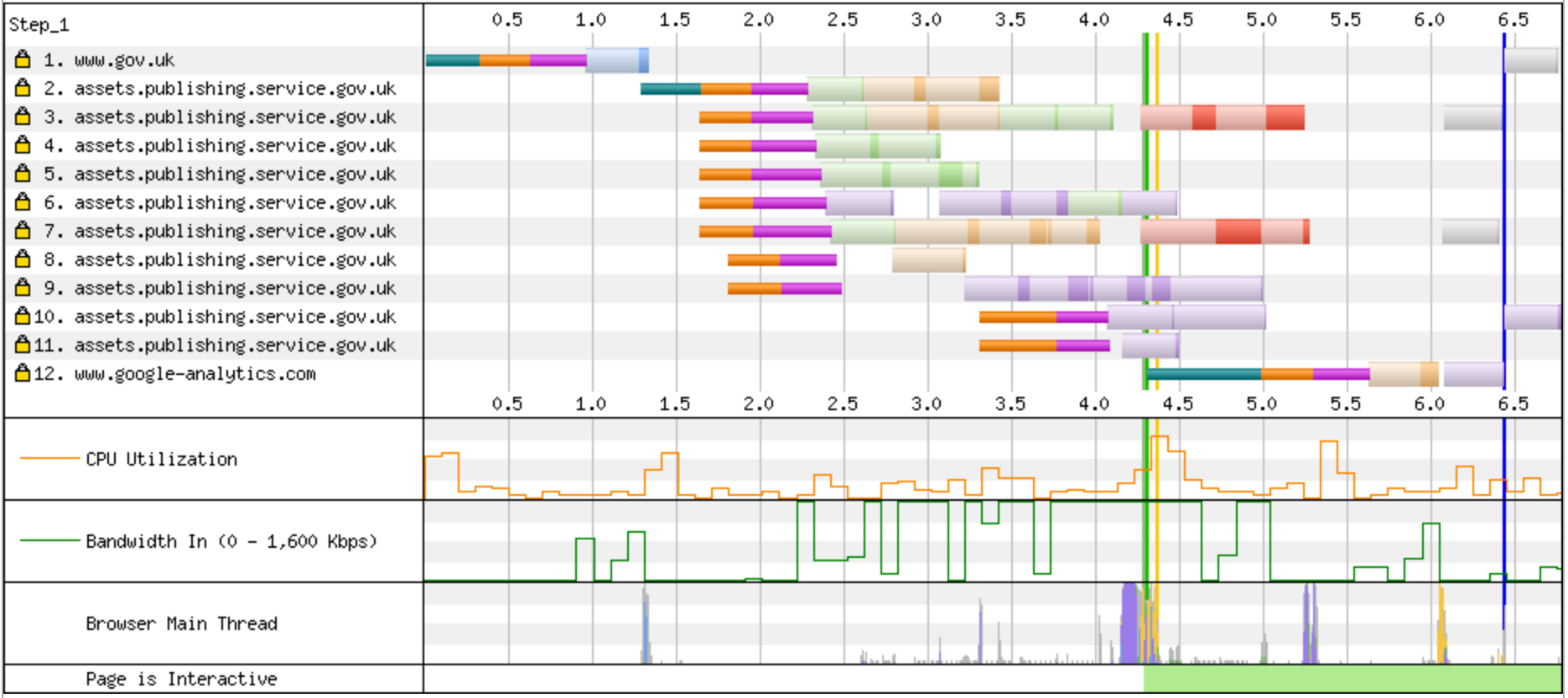
Running Web Page Test (WPT) against a number of pages across GOV.UK reveals that the browser is having to open a greater number of TCP connections due to the use or SRI, and more specifically the crossorigin="anonymous" attribute attached to the CSS and JavaScript references. This attribute is mandatory for security against cross origin policy violations. The use of the crossorigin="anonymous" forces the browser to open a brand new TCP connection to ensure that no user credentials are shared across the connection. This can be seen in the images below:
Homepage
In this example 11 TCP connections are being opened when the browser default for HTTP/1.1 in many browsers is 6. Since opening TCP connections is expensive, this will be having a negative effect on performance.
Full test can no longer be seen due to WebPageTest being sold to CatchPoint.
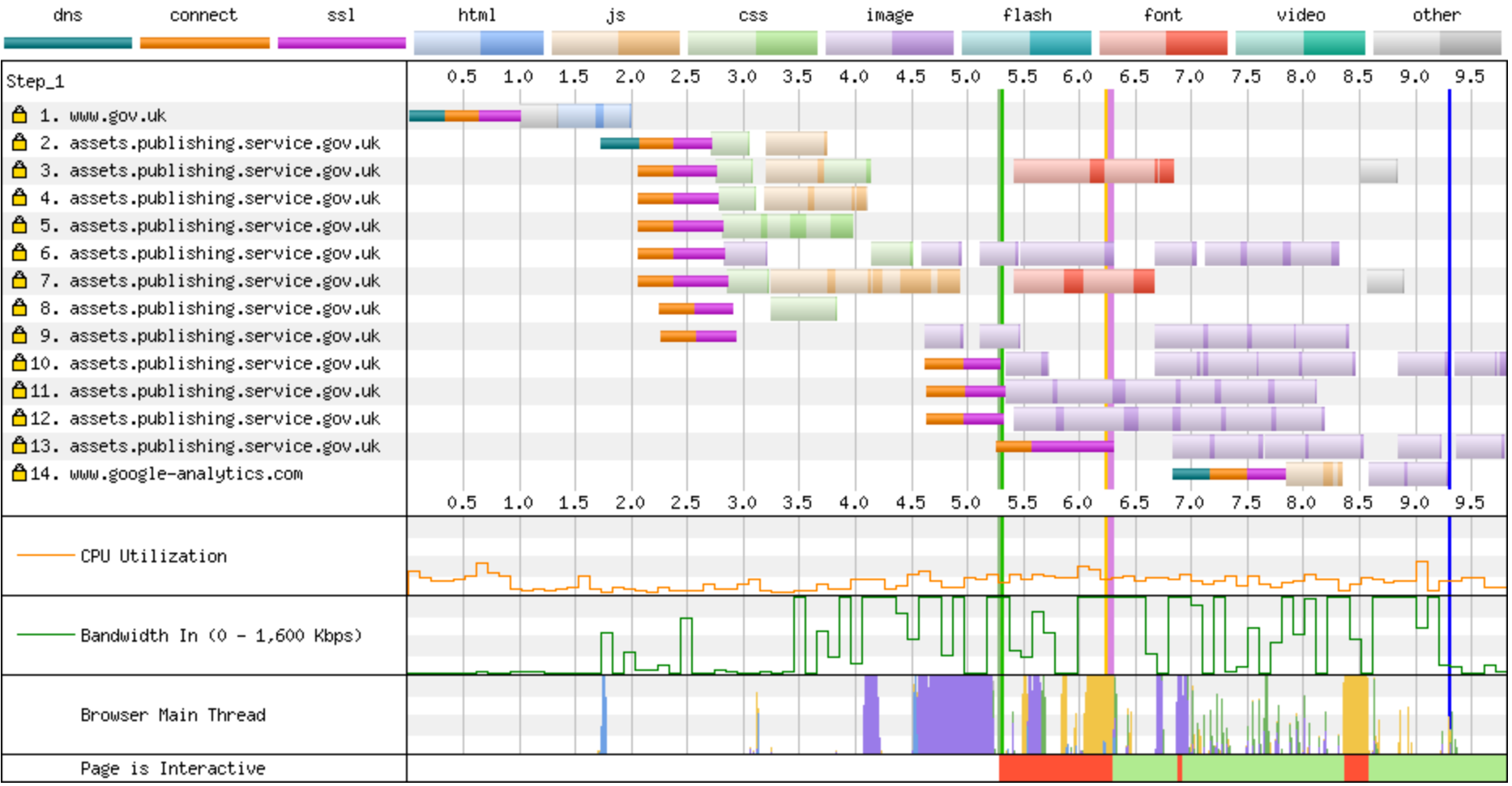
Past Prime Ministers page
The same issue can be seen on the Past Prime ministers page, where 13 TCP connections are opened instead of the default 6 a browser usually does. As can be seen in the bandwidth graph the connection isn’t being fully utilised, this is probably due to the TCP slow start is an algorithm that each TCP connection uses.
Full test can no longer be seen due to WebPageTest being sold to CatchPoint.
HTML size
A very minor point, but adding the crossorigin="anonymous" integrity="sha256-wLi6ixZSqsrSmNdPJHUiYBh/U4tQxAwkhPfzM8vDzys=" to the 12 resource requests across a page could be adding an extra 1KB to the HTML size (although GZipping will minimise this).
HTTP/2
Will HTTP/2 solve this issue? Since HTTP/2 multiplexes assets over different streams on a single TCP connection. Unfortunately not. Requests without credentials use a separate connection as mentioned in the article here. So even when we eventually enable HTTP/2 we will have the same issue where an anonymous connection will be opened.
Proposal
I’m proposing we disable SRI for all assets from the https://assets.publishing.service.gov.uk domain. Since this is a domain under our control it is highly unlikely that a MITM attack will occur. Assuming an attacker gets that far they would most likely be able bring the whole site down anyway due to the level of access they would need. Removing SRI will then allow us to remove the mandatory crossorigin="anonymous", which will then allow the browser to open and reuse connections as they are intended (and hit the maximum of 6 connections).
For assets that do come from a third-party domain, they should still have SRI enabled for security reasons.
